
A unique group or personal key access level is created for every user. The access level represents a combination of keys or hierarchic lists of keys and a reference to a time period.
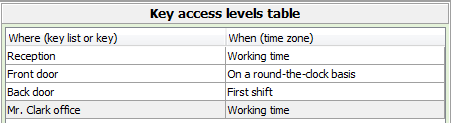
Key access levels have a field "Time interval". Time intervals may include 10 time periods that are time, week day, holiday, weekend, even-odd day, and an individual list of days. If more than 10 time intervals are needed, you can add an entry in the access level, and there are no limitations in a number of entries.
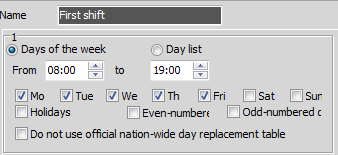
You can assign, in addition to individual time, an individual list of work days. For instance, you can create the list "First work day", so that an employee can have access to the equipment room in order to do the maintenance work on the first work day of the month. All lists are registered in a key management system message log. Entries are made in the message log whether or not servers are connected with a software. The software is only needed for creating a database and generating reports.
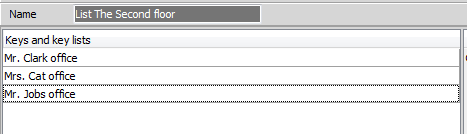
An electronic key holder KeyGuard understands hierarchic lists of keys (groups). This means you can create a list of keys, which, for its part, includes nesting lists (up to 7 nesting levels). Each list has its own name. You need to include this list in the key access level of a user in order to give keys according to the list. If keys are returned, you have to select a section for work with lists in the key holder menu, select a required list from the table and get keys back.
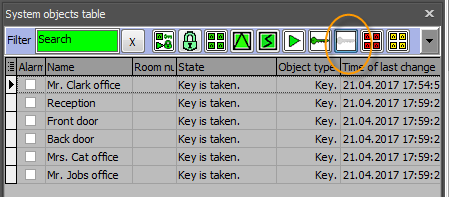
Open the "Table of system objects" and push the quick filter button "Given keys" in the software. The system will filter the list and leave only the keys that are not returned at the moment. Additional information about last events - who has taken and returned a key and when, quick filter, etc. - is also shown here.
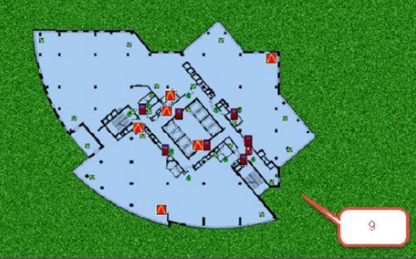
In addition, the system works with graphic plans of the object, this helps to put key signs onto the plan and visually control the status of keys, with reference to single levels and rooms of the object.
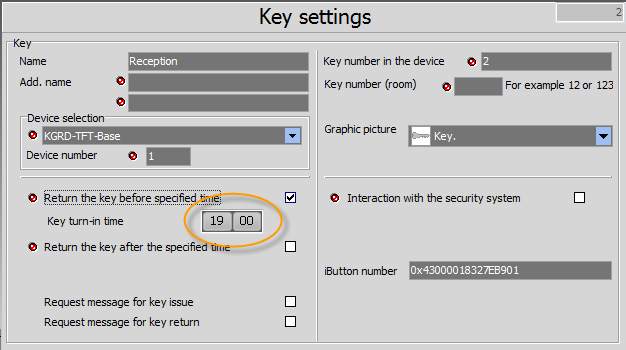
You can specify in the settings of a key that a key has to be returned in the key control system KeyGuard until certain time or within a certain period of time. If a key is not returned within a period of time set, the system activates alarm. Alarm can both be displayed on the screen of the monitoring system and can be sent automatically, in form of an SMS, to telephone number saved in the system or specified in the settings of the email.
1. If you are allowed to take only one key, you just have to put the card on the right reader. If there is a key in the storage cell, the system will immediately open the door and backlight the cell with your key.
2. If you have the right to take several keys, the system will display the menu with the table where your keys are listed. You can scroll through the table page by page or use filter or search keys. The system highlights chosen keys, given keys, blocked keys, keys forbidden for this time period, etc.
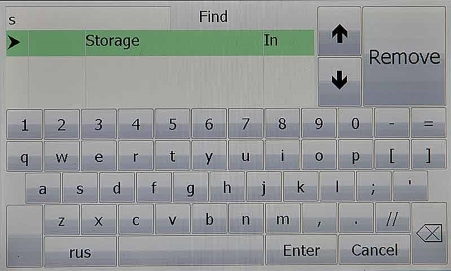
3. You can perform a key search both according to the key name and according to the room number. Simply enter first digits (symbols), and the system will filter the table.
4. With a finger print reader you have an option to assign the different keys to the different fingers. Just present you right finger and you will get the appropriate key at once.
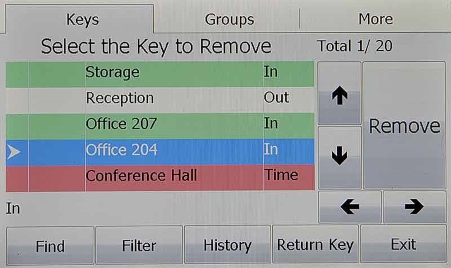
Every key may have a name and a number. The key number consists of digits but can have one letter of the Latin alphabet, at the end, e.g. 101A, 101B. The search can be performed by the name and by the number. Just enter any symbols. All coinciding variants will be filtered and displayed on the screen. You can activate the command for giving the key, directly from the search menu, or return back to the main menu to continue work.
This information is available directly in the panel of the key holder. Put your card on the reader, choose the required key in the table (of course, you shall have permission for this key), push the "History" button. 16 last events regarding the key will be shown. Events include action, time, surname and given names, and telephone number of an employee. Reports for a longer period of time are also available in the software.
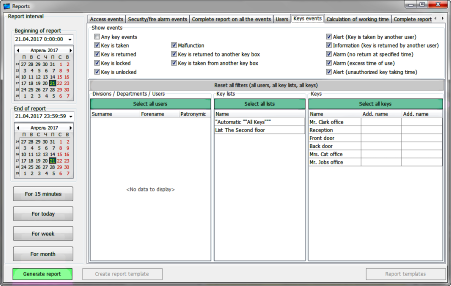
16 last events are available directly in the panel of the key holder. You can view a more detailed report in the software. Select a key or a list of keys, select a department or a particular user, and select a time interval. You can export a report to files in different formats or print a report. You can also save a report as a template and start it automatically.
You can calculate work time using the software, including for employees with the right to take keys. In this case, all employees have to register their leaving/coming on the readers of the key holder. Calculated work time can be displayed online on the screen of the key holder.
The software uses a free FireBird database. The database is protected with a password. We recommend you to use encryption for responsible applications, with the help of standard or other Windows tools.
As in the case of every other security system, we do not recommend to have direct access to unprotected networks. The system has a certain level of protection, but, if you use insecure channels, it is strictly recommended to provide protection with any standard aids (VPN channel and other).
The total number of memory cells is 200 000. The number of memory cells may be increased when you order the equipment. You can change distribution of this memory between users and events by yourself. For instance, you can allot 100 000 cells for the storage of user data and other configuration and 100 000 cells for the storage of events.
The system also has memory of events for every key, i.e. the system stores last events for every key, irrespectively of how long ago this event took place.
The system allows to switch between interface languages online. Simply specify a language in the access card settings, and the screen language will change automatically, depending on an access card used.
We supply systems with a solid steel door with a thickness of 2 mm for a 50-key system and with a thickness of 1.5 mm for a 100-key system.
The transparent door is made from polycarbonate - the most durable material of all transparent plastic materials. We also supply solid metal doors.
Yes, we supply key holders without doors.
We supply in two colours for your choice: dark silver 5359AO445 and light RAL7038. Upon request, we also manufacture electronic key holders in a colour according to your specification.
Yes, two brackets are included in the scope of supply - one for fixing under an angle of 45 degrees in the lower part of the key holder, the second one for fixing on the right side of the housing.
The power supply of the system is provided via an electric socket and could be any international range 100V - 250V), maximum energy consumption is 60 W. Electric batteries are included in the scope of supply, battery life is up to 20 hours. The system automatically charges and tests electric batteries. The electronic key holder KeyGuard constantly monitors the state of electric batteries and, if the capacity of batteries by and by decreases to a critical level, the system will display a battery failure and a message about a need of battery replacement.
If the main power supply is shut down, and the batteries are discharged, the system will remain blocked. In order to get the keys, you will have to open the door lock with an emergency unlocking key, unscrew two inner door fixing screws, open the inner door lock with the same key, and unblock key clusters by pulling the pins standing out from the solenoids.
The rotary column of the door does not allow to fully bury the key holder in the wall. You can install the key holder so that its housing will stand out of the wall to 55 mm. Do not hesitate to contact us if you need decorative mouldings for such installation.
Assembly of the system is quite simple. You can start the system by yourself.
1. Please make sure that a wall where the key holder shall be mounted will withstand the load of 40 kg (100 LBS).
2. Drill 4 holes and hang the main unit.
3. Screw one of the two brackets included in the scope of supply (for installation from below or for mounting from the right side of the housing) and connect the control panel (one connector).
4. Connect the system to 100 - 220V power supply, to grounding and put on the battery terminal.
5. Start the system setup mode (button on the plate of the control panel inside the main unit), enter the IP addresses of the system and the server (see manual).
Programming is performed with the help of the software included in the scope of supply (watch video tutorials on our website).
The key management system is not a safe. However, we have taken some measures in order to prevent unauthorized opening. The door is equipped with a sensor, the lock cylinder is made from HSS and has drilling protection. The lock is additionally protected with an attachable panel. We recommend you to integrate the key control system with a security alarm system, to provide security at the object. In this case, only authorized access to the system will give a command to switch off the security alarm, and unauthorized access will activate the alarm.
The system has double protection from unauthorized opening. A main magnetic contact shows the position of the door, and an additional magnetic contact analyses the outside magnetic field. Shall a burglar try to by-pass an inside magnetic contact detector by an external magnet, the additional contact will be triggered. You can connect the alarm output to the object security system or see the alarm go off, in an alarm monitoring software.
The key holder is equipped with 5 outputs (4 optical-coupled solid-state relays and one relay rated of 250V 5A). You can adjust each output to be activated after a particular event: door opening, taking / returning a key, etc.
We supply two-format readers supporting EmMarin and HID proxCard2 (125 khz) formats simultaneously. Installation of MiFare readers is also possible. Readers of other formats can also be connected without any help. For this purpose, the system has two Wiegand interfaces with a format from 26 bits to 80 bits.
If several employees work in a room, and the first employee has taken a key in the morning, the system will not know for the second employee whether he or she would like to take or to return a key that has not been returned. In this case, you have to push additional buttons on the touch screen, it will take more time. The simple calculation shows that, if the key management system is used intensively, work time losses will be over thousands US dollars during 10 years of use. We have removed the need to push extra buttons and time losses. Everything is easy - left reader for returning keys, right reader for taking keys. At the same time, you always have the possibility of control using the display keyboard.
Keys are attached to key fobs by a 3mm one-use clamp made from stainless steel. The key is put on the clamp and slapped inside the key fob. You cannot remove the key from the key fob unless you break either a key or a clamp.
Key fobs are developed taking into consideration the fact that keys can be replaced or added many times. For this purpose, you need to file the clamp directly near the key fob, take a new clamp, put required keys on it, and insert the clamp into the key fob, pushing a piece of the old clamp inside the key fob. You can replace up to 5 clamps depending on the length of the remaining clamp pieces.
Display backlighting has quite big energy consumption and is off when the system is switched in the battery operation mode. If you want to activate the system backlighting, touch the screen or put the card on the reader. The screen backlighting is switched on.
Companies where a number of employees with access to keys is limited have a possibility to use KGRD-0012 modules for 12 cells, WITHOUT key fob fixation. In this case, only a system door will be blocked. An employee passes through authorization and may take only his or her key. If he or she has taken a someone else's key, an alarm signal will be generated. All reports on who has taken/returned a key are available in the software or in the key holder panel. The system without key fob blocking at the slots is significantly cheaper. Areas of application: car traders, keys for cash terminals, keys for equipment rooms (switchboard rooms), etc.
Our system can store keys both in cases and with key fobs. However, if keys are stored in cases, they are attached to special key fobs with a little greater depth than standard ones, and only after that they are inserted in the sealable cases. Thus, we guarantee the presence of the key in a case. You can choose scope of supply for cases, depending on the size of keys used.
Units have a fixed number of slots - 3, 5, and 10. You can order an incomplete set of modules in units. In this case, empty spaces will be closed by stainless steel covers.
Each control panel can be connected to up to 20 units with a total number of up to 2,000 keys, i.e. you will need for the storage of 3,000 keys two systems for 1,500 keys each. However, if they will be in one place, the can be connected via Ethernet. In this case, you do not need to remember in which system your key is stored. You can log in and give a command to give a key, in any system.
The standard connection interface is Ethernet. There are also RS-485 and RS-232 galvanic isolated interfaces. The initial setup of the system and the server IP addresses is carried out in the service menu of the electronic key holder.
MorphoSmart finger print scanner from the worldwide biometric technology leader, French company "Safran", are integrated in the display housing.
You can define any access type: only with a user number and password, only with a card, combined access with a card and password confirmation or you can also use biometric reader.
Yes it is possible.
The warranty period is 5 years.
If the system is used very intensively, and some mechanical parts such as lock, electric lock, and loops of the system break down, after the end of the warranty period of 5 years, call us, and we will send replacement for free or at a nominal fee.
This is a very important question. The system uses the energy-independent memory in different technologies - the DataFlash memory is used for the storage of data about users and key access levels, this Flash memory essentially differs from the USB flash drives known to everybody. This memory type has a microscopic size of pages with guaranteed recording quality. Such speciality helps to change the data of a particular user, without serious consequences and without a need to overwrite the remaining data, thus helping not to worry about limitations related to the number of cycles of rewriting in the Flash technology known to everybody.
Special ferromagnetic memory, with an unlimited number of cycles of rewriting, is used for the intermediate storage of events. Thus, we guarantee problem-free system functioning at any load within the entire life time.
The system is designed for continuous operation during many years. All components are selected with a certain factor of safety and used at reduced loads. For instance, an ultra-bright display functions at only 50% brightness (two times longer service life), other components also work at lower voltage or at 10-20% less than the capacity specified. The service life of the KeyGuard key storage system is 15 and more years.
Service maintenance is not needed, unless you use the system in factory conditions, i.e. keys and key fobs are stored directly in shops. The likelihood is that the system can be contaminated, and, in this case, in order to clean the contacts, you need to wipe them with a cotton wool pad moistened with alcohol.

To the top